OSS Risks
In addition to identifying open source vulnerabilities based on CVEs, Qwiet AI by Harness also detects OSS Risks associated with your dependencies that can compromise your application's security.
Why OSS Risks detection is important
When you include open-source packages in your application, you take on risks beyond just known CVEs. Packages can be malicious, abandoned, or susceptible to supply chain attacks. These risks are often harder to detect than traditional vulnerabilities because they may not have associated CVE entries.
To mitigate such security issues, you need visibility into the overall health and trustworthiness of your dependencies. Qwiet AI by Harness helps you identify these risks so you can make informed decisions about which packages to include in your application.
How Qwiet AI by Harness can help
The Qwiet AI by Harness OSS Risks feature detects the following categories of OSS risk types:
Malicious Package
A malicious package is an open-source package that has been identified as containing intentionally harmful code. These packages may:
- Steal sensitive data such as credentials, API keys, or environment variables
- Install backdoors or remote access tools
- Execute cryptocurrency miners
- Exfiltrate source code or intellectual property
Malicious packages are often distributed through package registries by attackers who create new packages or compromise existing ones. Qwiet AI by Harness flags these packages so you can remove them from your application immediately.
Supported package ecosystems: gem, npm, nuget, pypi
Abandoned Package
An abandoned package is one that is no longer actively maintained by its original authors. Using abandoned packages poses security risks because:
- Security vulnerabilities discovered after abandonment will not be patched
- Compatibility issues with newer language versions or dependencies won't be addressed
- The package may become a target for repository hijacking
When an abandoned package is detected, consider finding an actively maintained alternative or forking the package to maintain it yourself.
Supported package ecosystems: golang
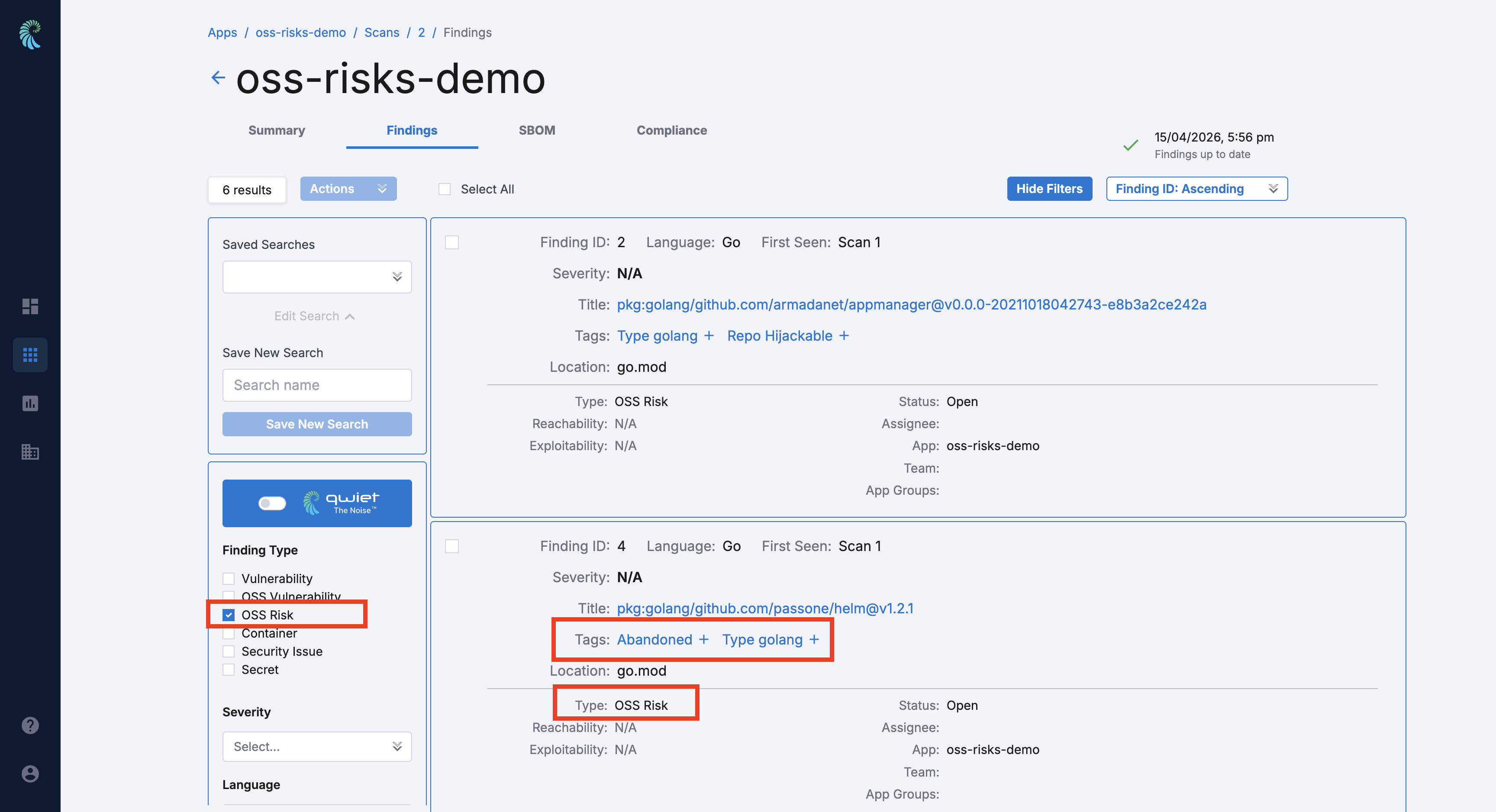
Hijackable Repository
A hijackable repository refers to a package whose source repository could potentially be taken over by an attacker. This can occur when:
- The original maintainer's account is deleted or expired
- The repository namespace becomes available for registration
- The package references a repository that no longer exists
If an attacker gains control of a hijackable repository, they could push malicious updates that would be distributed to all users of the package.
Supported package ecosystems: golang
Typosquatting
Typosquatting is a technique where attackers create packages with names that are intentionally similar to popular, legitimate packages. These malicious packages rely on developers making typos when installing dependencies. For example:
lodashvs1odash(number one instead of letter L)requestsvsreqeusts(transposed letters)expressvsexpres(missing letter)
Typosquatting packages often contain malicious code that executes during installation or runtime. Qwiet AI by Harness detects these suspicious packages and alerts you to verify you're using the intended package.
Supported package ecosystems: gem, golang, npm, nuget, pypi
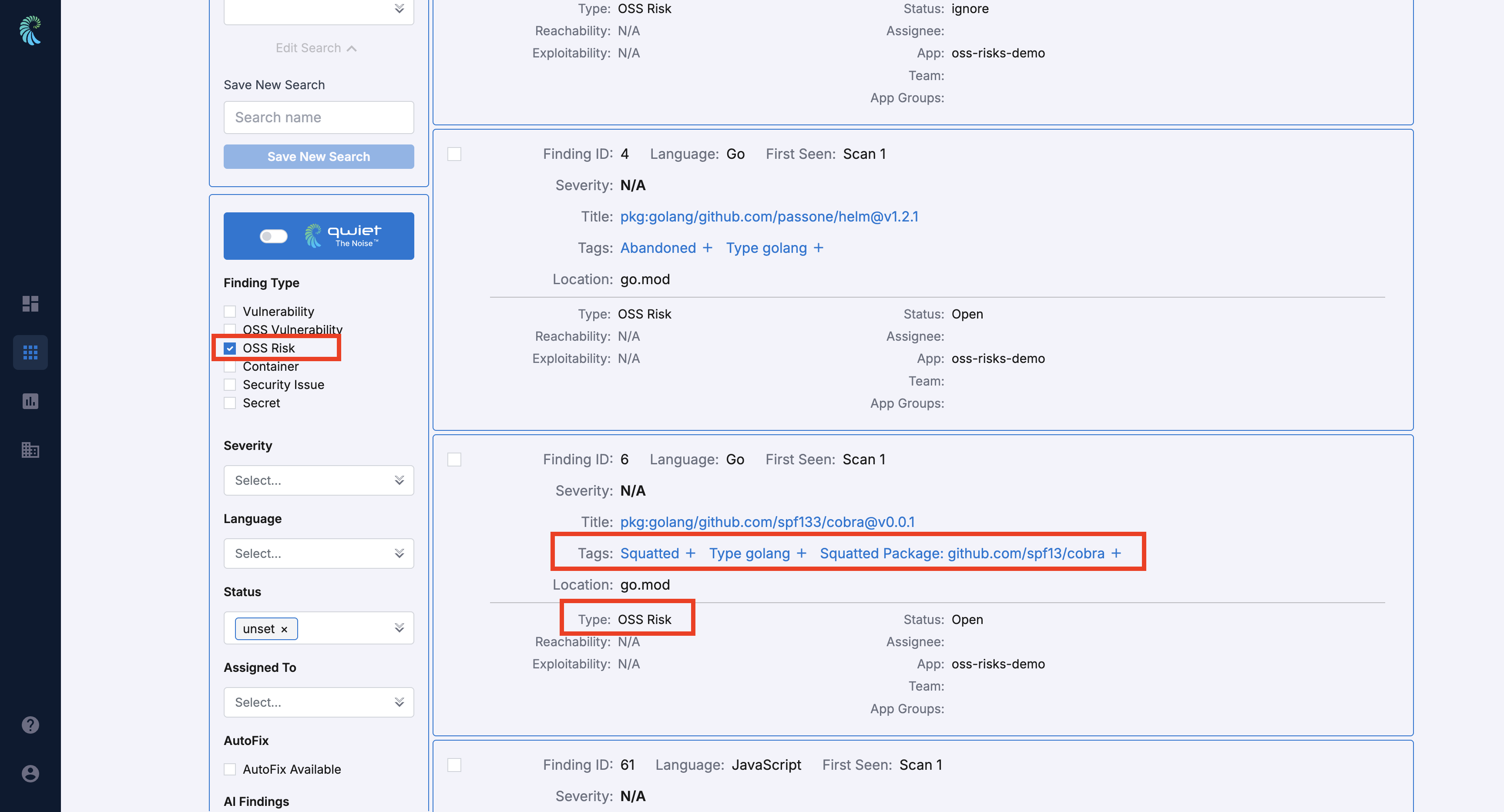
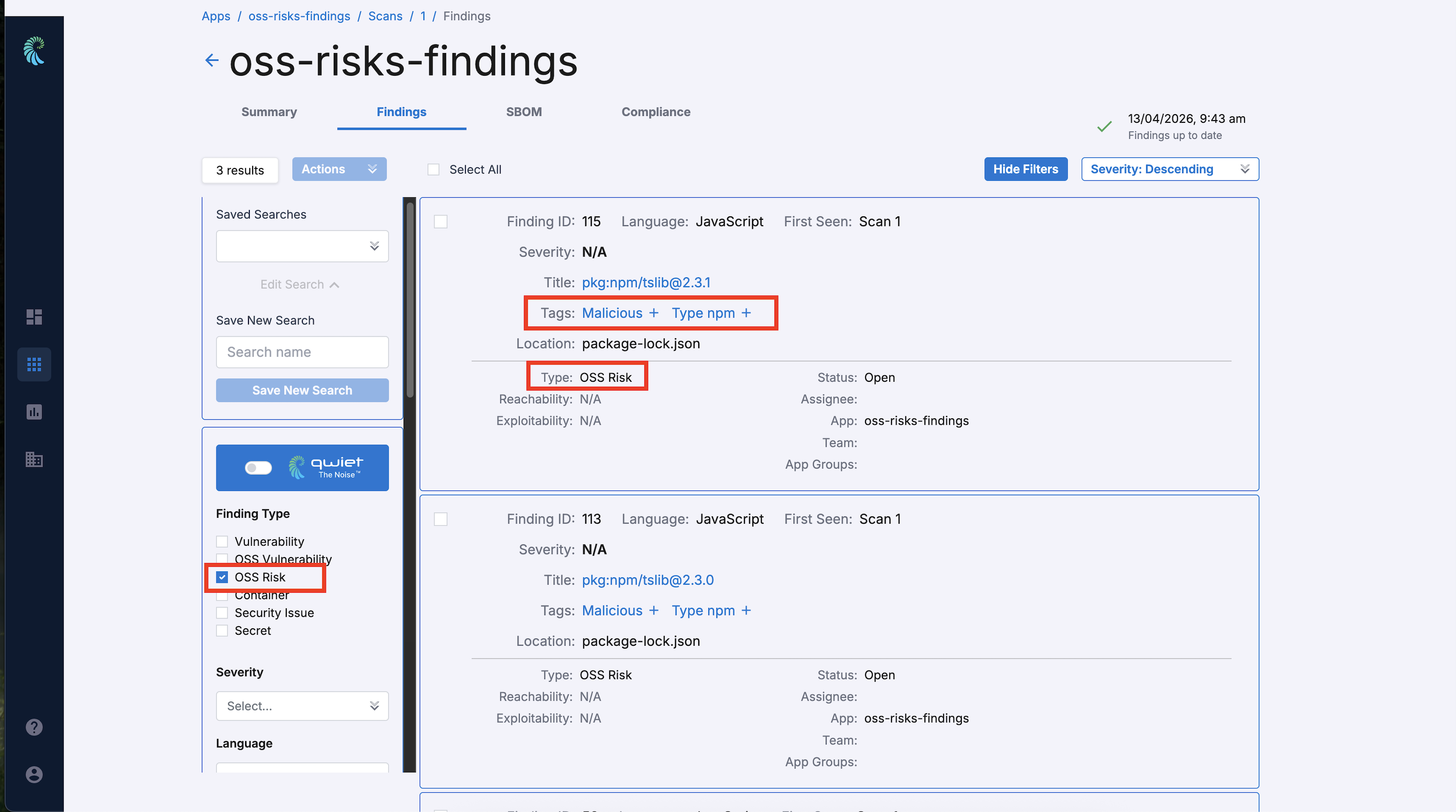
Viewing your results
The OSS Risks that Qwiet identifies in your application will appear in the Vulnerabilities column alongside CVE-based findings.
To access your results:
- Log in to the Qwiet Dashboard
- In the list of Applications, find the one you're interested in and click to open.
You will see a summary page of all vulnerabilities identified by Qwiet, including OSS Risks. Click the Findings tab to display a list of the issues identified. You can filter the list to show only OSS Risk findings.